|
0 Comments
We realize that 2020 was an extremely challenging year for everyone, and I am confident that the majority of us are looking forward to 2021. The COVID-19 virus affected many businesses across the country, and unfortunately it directly impacted a number of our local clients. Our company typically specialises in all types of security. However, we can also assist you with multiple layers of COVID screening if needed.
We were all hoping that the new year would bring us closer to eliminating this pandemic, but unfortunately it looks like it may take a little longer than anticipated. This virus has changed the way companies do business on a daily basis. We realize the extra efforts that businesses are taking to ensure the health and safety of their employees. Over the past 9 months Capital Asset Protection has assisted our clients with the difficult task of screening all employees, vendors, and visitors entering their facilities. These daily screenings have enabled our clients to remain open for business, and provide their employees with job security during these difficult times. 2021 may bring additional challenges, but hopefully it will also bring additional opportunities. If you feel that our company may be able to assist with your current security structure, or your COVID Screening, please don’t hesitate to contact us. You can contact Mark Drear at 412-812-5661, or [email protected] Capital Asset Protection hopes for a safe, secure, and happy holiday for all of our employees, clients, and associates.
COVID-19 Screening
Capital Asset Protection is a privately owned contract security company that has been servicing the tri-state area for the past 27 years. We specialize in providing well trained, professional security officers to a number of our industrial and manufacturing clients, commercial real estate, schools, hospitals, coal and gas exploration, and hospitality venues. 2020 has been a difficult year for everyone, and we have all had to make certain sacrifices in order to deal with the COVID-19 epidemic. One way that we have been able to better serve our clients has been for us to provide COVID-19 Screeners to their facilities. Our screeners assist them by asking the COVID questions to all employees entering their facilities, and we also take temperature readings of all employees. These Screeners are employees of Capital Asset Protection, and they must all go through the same hiring criteria that our Security Officers do. This includes the completion of all state required paperwork, background checks, drug testing, and extensive COVID training. If your company is currently utilizing Screeners to deal with the COVID-19 epidemic, and you think that we may be able to assist you. Please don’t hesitate to contact us. You can contact Mark Drear at 412-812-5661, or [email protected] Labor Day is the opportunity for employers and employees to be rewarded for their efforts and hard work. We hope that you enjoy a safe and secure Labor Day weekend with family and friends.
 As you may know, all employees are required to wear a mask to work in Pennsylvania starting tonight at 8 PM. Capital Asset Protection Inc is sourcing masks for all employees but will not have possession of them for a few days. Please provide your own mask for the next few days. We will distribute ours as soon as they arrive. From our governor: Masks must be worn by workers and customers at businesses that are continuing to operate in Pennsylvania under an order signed by the state health secretary Wednesday. The order, which is in now effect, is set to be enforced starting at 8 p.m. Sunday. It requires businesses to deny entry to customers who do not wear masks, "unless the business is providing medication, medical supplies, or food, in which case the business must provide alternative methods of pick-up or delivery of such goods," Thanks, and stay safe. Dan Aloe President Hi
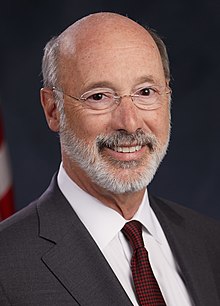
I hope that you and your family are doing well during these extremely difficult times. The COVID-19 epidemic is something that is new to everyone, and the uncertainty is scary to all. Security is one of the businesses that the Governor has determined to be essential, and we are committed to continuing our service to our clients throughout the area. Some have contacted us to increase their ongoing security, while other companies that have never utilized security in the past, are calling us to evaluate their options. Everyone has been affected by this virus in many different ways. If there is anything that we can do to assist you or your employees during these difficult times, please don’t hesitate to contact us. Thanks, and stay safe. Mark Drear Vice President 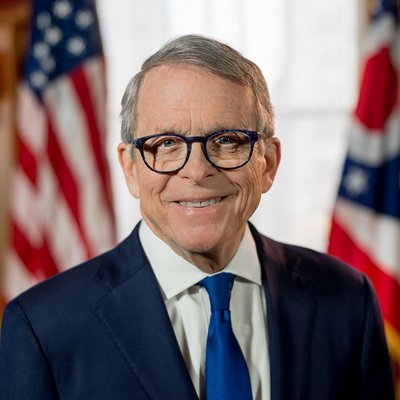 COVID-19 Work Schedule Update: Both Governor DeWine (OH) and Governor Wolf (PA) have issued Stay-At-Home orders. Both orders for each respective state should be followed to help contain the spread of COVID-19. These orders do not effect your employment with CAP or your work schedule. Security has been listed as an essential business and we will continue to operate as usual until further notice. You do not need a letter from your employer to travel to or from work at this time. At CAP, we are closely monitoring updates and information available on the spread of the COVID-19 virus. Protecting our employees while mitigating disruption to our customers is the top priority. We are following the guidance for business and employers for coronavirus disease (COVID-19) of the CDC (Center for Disease Control) to reduce the spread of the virus in our community as well as in our offices. At this time, CAP has not been directly impacted by the virus, nor have any of our partners indicated any impact by the pandemic. However, we will be working with our providers and communicating any updates as they become available in this ever-evolving situation. Employees who have symptoms of acute respiratory illness are recommended to stay home and not come to work until they are free of fever (100.4° F [37.8° C] or greater using an oral thermometer), signs of a fever, and any other symptoms for at least 24 hours, without the use of fever-reducing or other symptom-altering medicines (e.g. cough suppressants). Employees should notify their supervisor and stay home if they are sick. CDC recommends that employees who appear to have acute respiratory illness symptoms (i.e. cough, shortness of breath) upon arrival to work or become sick during the day should be separated from other employees and be sent home immediately. Sick employees should cover their noses and mouths with a tissue when coughing or sneezing (or an elbow or shoulder if no tissue is available). Instruct employees to clean their hands often with an alcohol-based hand sanitizer that contains at least 60-95% alcohol, or wash their hands with soap and water for at least 20 seconds. Soap and water should be used preferentially if hands are visibly dirty. Visit the coughing and sneezing etiquette and clean hands webpage, staying home when sick, for more information. Employees who are well but who have a sick family member at home with COVID-19 should notify their supervisor and refer to CDC guidance for how to conduct a risk assessment of their potential exposure. |
Exploring What Creates A Protected World Archives
December 2023
Categories |






 RSS Feed
RSS Feed

